Cal AI, a popular calorie tracking app previously marketed by Mr. Beast, has suffered a data breach, with millions of user records being dumped on the darknet. While the exposed data isn't highly sensitive, it includes personal information that could potentially be exploited by scammers for targeted attacks. The attack comes just a week after Cal AI was acquired by the much larger firm MyFitnessPal.
About Cal AI
Developed by an ambitious teenager named Zach Yadegari, Cal AI aimed to help users easily and accurately track their daily calorie intake. Users could simply take photos of their meals, and the app would analyze the image, identify the contents, estimate portion sizes, and calculate a rough calorie intake. The app also included a barcode scanning feature, along with other tools to streamline calorie data collection (Some users have claimed that the AI's calorie calculations are inaccurate). After an initial period of success, the young entrepreneur sold his startup to MyFitnessPal, a much larger fitness-focused tech company, for $40 million.
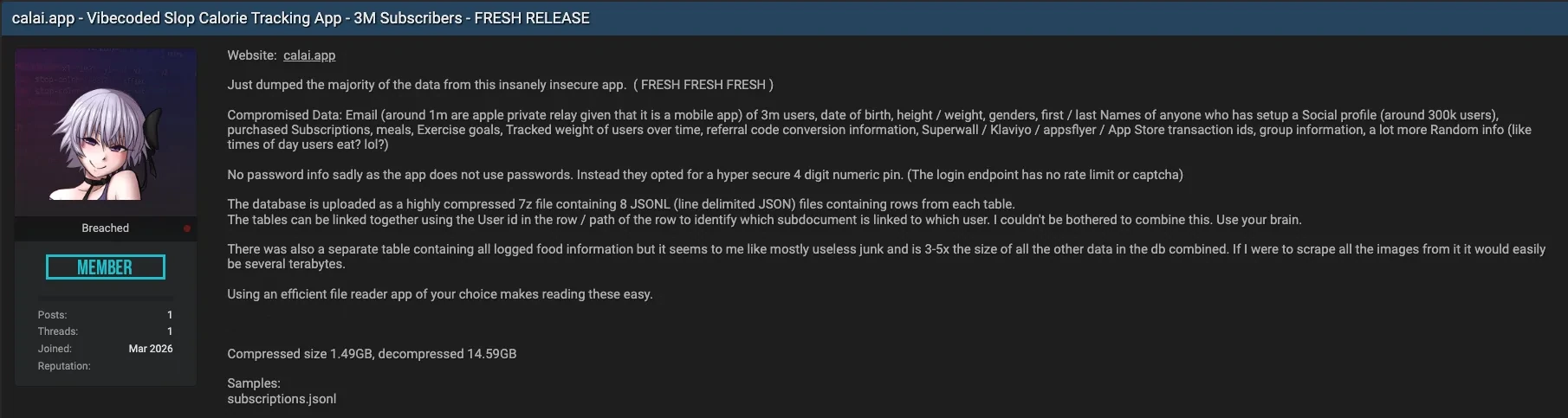
Uncovering the Breach
News of the breach first emerged about a day ago when darknet users discovered the data being dumped on illegal hacking forums. The attacker claimed that the app was highly insecure, which led to the breach. The dumped data totals just over 14GB and includes records of more than 3 million users. These records contain email addresses, full names, dates of birth, gender, and some health data collected by the app. The attacker also noted, “No password info, sadly, as the app does not use passwords. Instead, they opted for a hyper-secure 4-digit numeric PIN. The login endpoint has no rate limit or captcha.”
Conclusion
This latest breach should come as no surprise, given the era we live in. Whenever a company handles any data, any exposed or unprotected piece of infrastructure is bound to be exploited eventually. We're in a time where threat actors target anything unsecured, regardless of who owns it. Additionally, one could argue that this breach comes at an especially unfortunate time, as the company was only acquired a week ago. As of now, the company has not commented on the situation.





























0 Comments