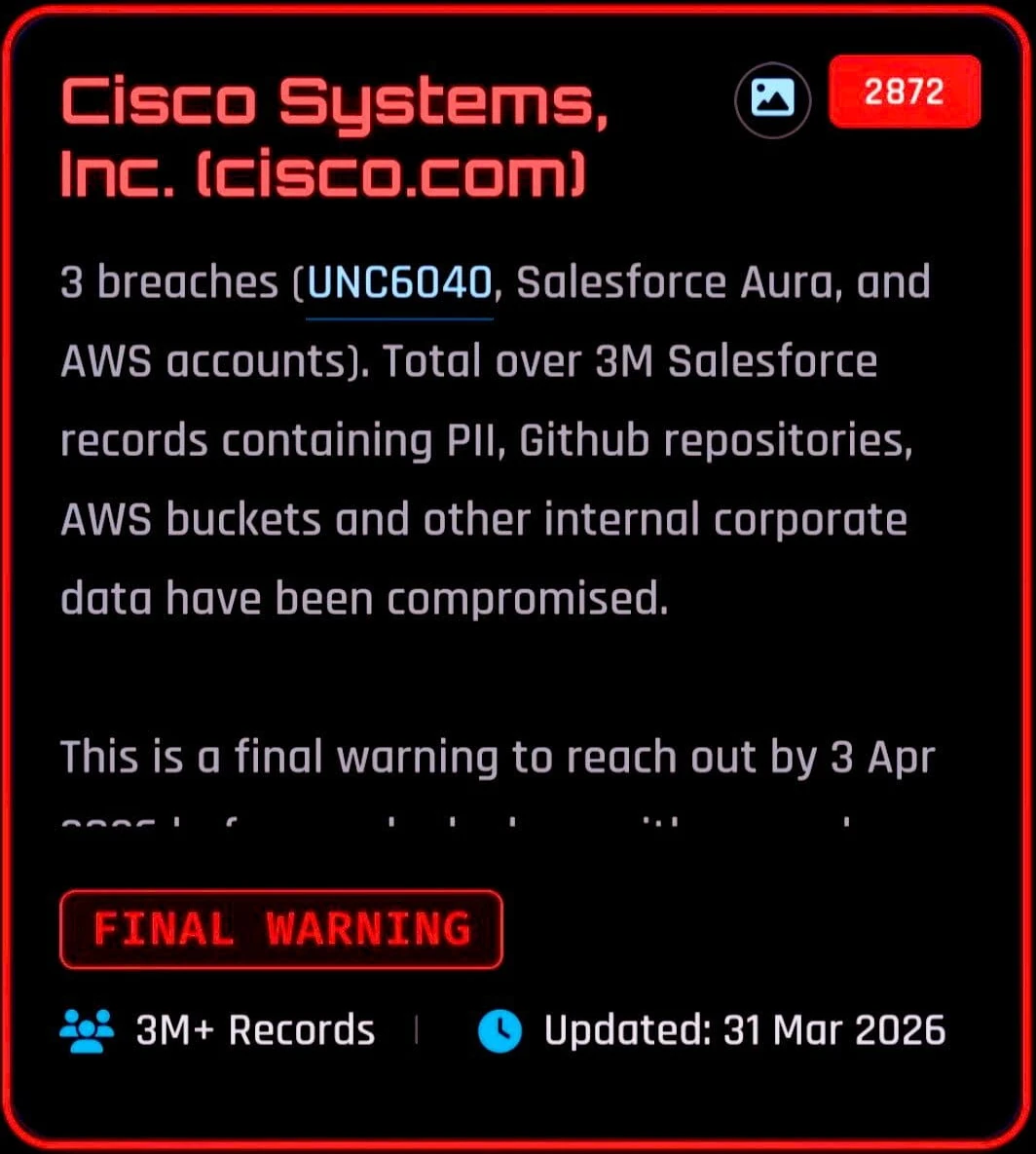
A recent set of claims attributed to the cybercriminal group ShinyHunters alleges a significant data compromise involving Cisco Systems, with reports referencing more than 3 million records tied to Salesforce environments as well as potential exposure across GitHub repositories and AWS infrastructure. The claims, which have not been independently verified, were accompanied by extortion demands and a deadline reportedly set for April 3, 2026, threatening further disclosure if negotiations do not occur.
Extortion Claims
According to statements attributed to ShinyHunters on a dark web leak site, the group claims to have combined data from multiple intrusion paths affecting Cisco-related systems. These include Salesforce CRM and Salesforce Aura environments, alongside AWS accounts and internal development repositories.
The attackers further assert that the total dataset exceeds 3 million Salesforce records containing personally identifiable information. In addition, references are made to GitHub repositories and cloud storage environments accessed during the same campaign. The claims suggest a broad compromise spanning both customer-related data and internal corporate assets, although no full dataset has been publicly released to substantiate these assertions.
Technical Entry Points and Access Methods
The reported intrusion narrative describes multiple entry vectors, including voice phishing (vishing) campaigns associated with the UNC6040 activity cluster. In these scenarios, employees are allegedly manipulated into authorizing malicious OAuth applications connected to Salesforce systems. Once granted, such tokens can provide persistent access without requiring repeated authentication, potentially bypassing standard security controls.
Further claims reference a second-stage activity cluster, often associated with UNC6395, where stolen OAuth tokens are allegedly used to extract additional credentials, including AWS keys and other secrets. These credentials may then be leveraged for broader access across cloud environments, depending on the scope of the compromised permissions. Reports also describe the use of automated scanning techniques targeting Salesforce Aura misconfigurations, suggesting that exposed guest access configurations may have played a role in at least part of the activity described by researchers.
Cloud Infrastructure Exposure
The extortion material reportedly includes screenshots said to originate from AWS environments. One image shows an EC2 Volumes dashboard containing multiple virtual drives with significant storage allocations and recent creation timestamps, dated around mid-March 2026. Another image reportedly shows an S3 bucket listing that appears consistent with Cisco-related naming conventions. While these visuals are presented as supporting evidence by the threat actors, they have not been independently validated, and no direct data samples have been publicly confirmed as part of the claims.
Additional Reporting
Separate reporting from Bleeping Computer suggests that a broader compromise may be linked to a supply chain issue involving the Trivy scanning tool ecosystem. According to those claims, a malicious modification to the “trivy-action” automation component was introduced, potentially enabling downstream access to multiple organizations.
In that context, it is reported that attackers were able to obtain AWS credentials and clone a large number of GitHub repositories, including projects described as AI-related and customer-associated systems. The same reporting suggests overlap between this incident and the ShinyHunters claims, although this linkage remains unconfirmed.
The compromise of Trivy-related tooling has also been associated with activity attributed to a group referred to as TeamPCP, which is described as having injected malicious code into development automation workflows, potentially affecting organizations relying on those pipelines.
Prior Security Disclosures and Context
Cisco has previously disclosed security incidents involving third-party systems and social engineering techniques. In one earlier case, a voice phishing attack reportedly led to unauthorized access to a third-party CRM environment used by the company, resulting in the export of a limited subset of profile-related information. At the time, Cisco stated that sensitive customer data was not impacted.
Separately, earlier claims in 2024 suggested exposure of internal development environments due to configuration issues, although Cisco indicated that core systems were not compromised in that instance. The current allegations arrive against this backdrop of prior exposure claims, though each incident differs in scope, attribution, and verification status.
Attribution, Uncertainty, and Response
The claims currently circulating are primarily based on statements from the threat actors and secondary reporting by cybersecurity researchers and media outlets. Some researchers have noted that while the screenshots and infrastructure references appear plausible, no definitive proof of full-scale data extraction has been publicly confirmed.
Cisco has not issued a detailed public confirmation addressing the latest extortion demands at the time of reporting. As with many incidents of this nature, verification remains dependent on further technical disclosure or official confirmation. In parallel with these developments, there has been increased governmental and regulatory attention on potential Cisco-related security exposure, including advisories urging organizations to apply security updates and review system configurations.
Conclusion
The situation surrounding the Cisco-related compromise remains unverified, with current information based on attacker claims, partial reporting, and cybersecurity analysis rather than confirmed forensic disclosure. While the reported scope suggests potential impact across cloud services, CRM systems, and development repositories, the absence of released data or official confirmation leaves significant uncertainty regarding the true extent of the incident. As investigations and analysis continue, attribution and technical validation will be key in determining whether the claims reflect a genuine large-scale breach or a partially substantiated extortion attempt.






























0 Comments