A major cybersecurity breach has recently impacted the Swedish government, targeting CGI Sverige, a global subsidiary of CGI Group, a firm that provides IT solutions around the globe. One of its main regional customers is the Swedish government. The attack was perpetrated by ByteToBreach, a relatively new cybercriminal group that managed to compromise critical systems developed for the Swedish government, including stealing the source code of Sweden’s E-Governance platform.
The Rise of E-Governance Platforms
E-governance platforms have been gaining significant popularity in recent years, with Europe emerging as one of the leaders in this space, rapidly adopting these systems. These platforms are essentially digital government portals designed to bring government services online. Tax services, paying fines, filing forms, and in some cases even voting and property transfers can all be handled through these systems. Tasks that previously required visiting a government office and filling out physical forms are now becoming available online. A user’s registration on these platforms is tied to their physical government ID, effectively creating a form of digital identity.
First Signs of Trouble
What makes this case concerning is that the breach was only identified after attackers published data taken from Sweden’s e-governance platform. This prompted an investigation by both Swedish authorities and CGI Sverige, which led to the discovery of the incident. ByteToBreach, the group behind the attack, published the stolen data on a darknet hacking forum. It is still unclear how the attackers gained access to the systems or what methods were used. In our opinion, this breach comes at a perfect time and serves as one of the strongest arguments against online ID verification systems, among other issues we will discuss later in the article.
Confirming the Breach
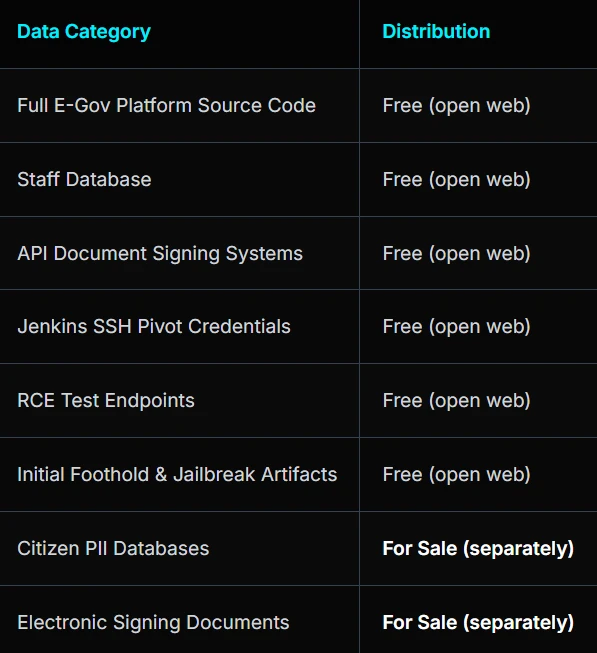
According to CGI Sverige, the company’s cybersecurity team first confirmed the attack after searching for and detecting abnormal activity on servers used for testing purposes. These servers contained older versions of Sweden’s e-governance platform, which allowed attackers to steal its source code. Despite this being a test environment and not used for production, reports suggest the breach could include an internal staff database, citizens’ personal information, electronic signing documents, and other sensitive data. This indicates that although it was a test environment, it was running a production copy of an older version of the application. Carl-Oskar Bohlin, Sweden’s defence minister, also personally confirmed the breach, stating that it is being investigated by the government and Sweden’s National Security Center.
Lack of Information & Data Concerns
While not uncommon in situations like this, especially in the early stages, details remain very unclear. The full scope of the breach has not been officially confirmed, and the only way to verify what may have been compromised for now is by reviewing the files published by the attackers. The company’s response, which states that only test servers and environments were compromised, appears to downplay the situation, as the attackers have published personal information belonging to both employees and regular citizens. According to reports, more than 10 million citizens were registered on the platform by 2024, and depending on how old that “test environment” is, many of these citizens could be affected.
As usual, breaches like this carry significant risks for both citizens and the platform itself. Fraudsters and other criminals could use the exposed personal information for advanced fraudulent campaigns, while attackers can analyze the platform’s source code to search for exploits and other attack vectors. Additionally, this breach raises broader questions about digital privacy. Europe is one of the global leaders in e-governance platforms and online ID verification legislation. Systems used for these purposes should be held to the highest standards, and when the government itself cannot protect such critical infrastructure, it should raise serious concerns.
Conclusion
As mentioned, many details are still lacking, and more information is expected to emerge over time. The full scope of the breach is currently being investigated to determine its impact on citizens. Swedish authorities now face a long process ahead, as hardening the affected platforms has become a necessity now that the source code is public. ByteToBreach typically operates with a profit motive, but it remains unclear what the exact purpose of this breach was or whether the group attempted to extort any of the parties involved.





























0 Comments