Europol and German authorities say a March 2026 operation called Operation Alice targeted a large network of fraudulent onion sites linked to the platform “Alice with Violence CP.” According to their public statements, the case began in mid-2021 and later expanded into a multinational action involving 23 countries. Officials claim the investigation moved beyond the alleged operator and led to the identification of hundreds of users who had interacted with the service. As with many high-profile law enforcement announcements tied to the darknet, much of what is publicly known at this stage comes directly from the agencies involved, and their framing naturally reflects enforcement priorities.
What authorities are claiming
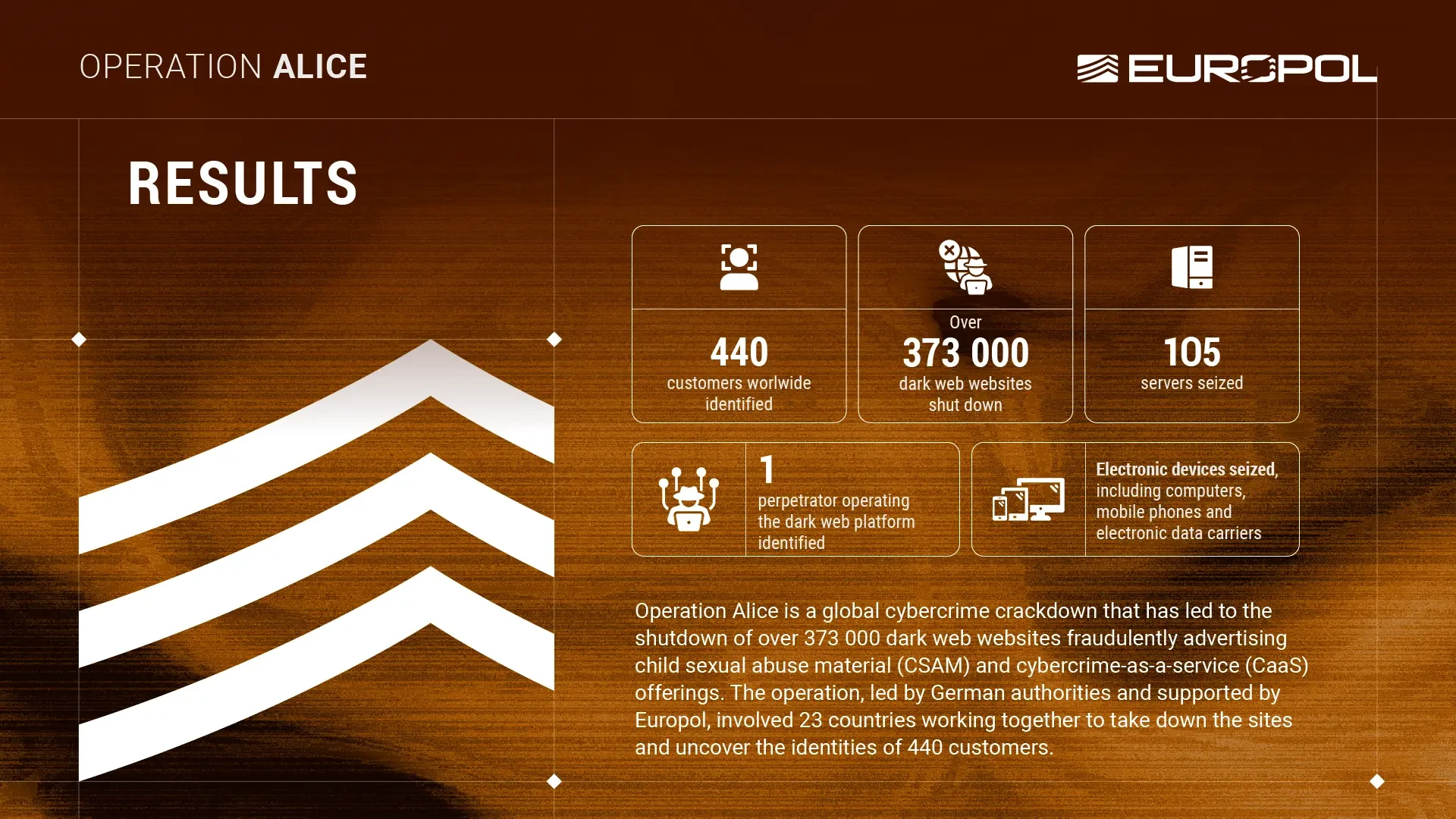
In their account of the case, Europol and German investigators say a single operator controlled more than 373,000 onion domains over several years. They describe the network as a large fraud scheme built around websites that advertised child sexual abuse material and various cybercrime-as-a-service offerings. According to those statements, the sites were set up to take payments, mainly in Bitcoin, without ever delivering the promised material or services.
Authorities further claim the operator used more than 90,000 of those onion domains to promote alleged CSAM packages between February 2020 and July 2025. Prices were said to range from EUR 17 to EUR 215, with listings promising anything from a few gigabytes to several terabytes of material. They also say the same infrastructure was used to advertise things like stolen credit card data and access to foreign systems.
The scale of the takedown
The headline figure in this case is the reported shutdown of more than 373,000 onion sites. That number is enormous by any standard, but it also raises the usual questions that come with darknet infrastructure counts. Law enforcement statements do not always make clear how many of these domains were unique active destinations, how many were mirrors, and how many may have been automatically generated or recycled over time. Even so, if the figures released by Europol are accurate, the case would point to a highly automated and unusually large onion-based network.
Authorities also say 105 servers were seized and that the wider infrastructure peaked at 287 servers, with 105 allegedly located in Germany. That server footprint appears to be one reason German agencies took the lead.
The operator and the wider investigation
German authorities say the suspected operator is a 35-year-old man based in China and that an international arrest warrant has been issued. They estimate he made more than EUR 345,000 from around 10,000 customers worldwide. Those figures come from investigators and have not been independently established in public reporting beyond the official releases.
Operation Alice reportedly ran from 9 to 19 March 2026 as an international action phase. Europol says that while the case initially focused on the alleged operator, investigators later identified 440 customers worldwide. The agency also says more than a hundred of those cases remain active.
The demand-side angle
One of the more significant parts of the case is that law enforcement did not frame this purely as a fraud operation. In the official version, people who attempted to purchase the advertised material became suspects themselves, even if the content was never delivered. Europol’s position is that the attempted purchases were enough to justify additional investigations, especially where investigators believed the users could provide leads in broader child exploitation cases.
That detail matters because it shows how these operations can evolve. A platform first presented as a scam network can still become the basis for a much wider user-identification campaign, particularly when the subject matter is as severe as this.
Europol’s Messaging
Europol’s statement was written in the familiar style of cross-border cybercrime announcements: large numbers, broad international participation, claims of strong coordination, and a clear deterrence message. The agency highlighted cryptocurrency tracing, server seizures, device seizures, and information sharing between countries. It also used the announcement to reinforce its broader child protection messaging and related projects.
That does not mean the claims are false, but it does mean the public version of the story is being delivered almost entirely through an enforcement lens. For readers used to darknet reporting, that distinction matters. Official statements are useful source material, but they are still official statements, and they are designed to present the operation in the strongest possible terms.
What stands out in this case
What makes this case unusual is not just the scale claimed by investigators, but the structure they describe. Rather than a straightforward marketplace delivering illegal goods, authorities say the network was built around fake listings and previews designed to take money from buyers without fulfilling orders. If accurate, that would make this less a conventional market and more a massive onion-based fraud machine built around highly criminal demand.
The other notable point is the sheer domain volume. More than 373,000 onion addresses suggests automation, duplication, or aggressive churn on a level that goes well beyond the typical single-service setup. Even allowing for inflated raw counts, it would still indicate a network designed for persistence and reach.
Conclusion
Based on the public record so far, Operation Alice appears to be another example of a darknet case where the official story is doing a lot of work at once. Europol and German authorities are presenting it as a major infrastructure takedown, a fraud case, and a user-identification operation rolled into one. Their statements describe a huge onion-domain network, a China-based suspect, and hundreds of identified users across multiple countries. Whether every headline number will hold up under deeper scrutiny is something that usually becomes clearer only much later. For now, what exists in the open is the law enforcement version of events, and that version is clearly intended to send a message well beyond this one case.






























0 Comments