A multinational law enforcement operation recently concluded with the dismantlement of SocksEscort, a large cybercriminal proxy network. The network hijacked nearly 370,000 residential routers, among other devices, setting up SOCKS proxies and selling access to the compromised networks. This allowed attackers to exploit legitimate residential IP addresses to conduct their cybercrimes. In addition to seizing domains and servers, authorities also confiscated $3.5 million in cryptocurrency.
About SocksEscort
SocksEscort was a massive global operation that, since 2020, hijacked over 369,000 devices. Targeting home routers and IP cameras, the service created a hidden network for use by criminals. By exploiting unpatched security flaws in popular brands like Netgear and TP-Link, the group turned everyday hardware into proxies, allowing criminals to use the network for their operations. However, by February 2026, the service had significantly dwindled, with only around 8,000 active connections remaining, including 2,500 in the U.S.
At the heart of the operation was a sophisticated malware called AVrecon, which gave attackers full remote control over infected devices. Many of the targeted routers were older models, no longer receiving security updates, making them easy prey. The FBI has released a list of the most commonly targeted equipment.
Used By Criminals
A proxy, while different from a VPN, functions similarly by tunneling your internet traffic through another network. This allows users to mask their real IP address and appear to be connecting from another location. For criminals, this provided the opportunity to buy access to residential IP addresses in specific regions, effectively masking their identity while committing crimes.
These residential IPs appear legitimate and clean, unlike traditional VPN or Tor exit node IPs, which are often flagged and associated with suspicious activity. This allows them to be used for more critical tasks, like financial fraud. Since the IP addresses belong to everyday users, there's a risk of implicating innocent civilians. Their devices could be hijacked and used for illegal purposes without their knowledge, potentially linking them to criminal activities.
The Investigation & Takedown
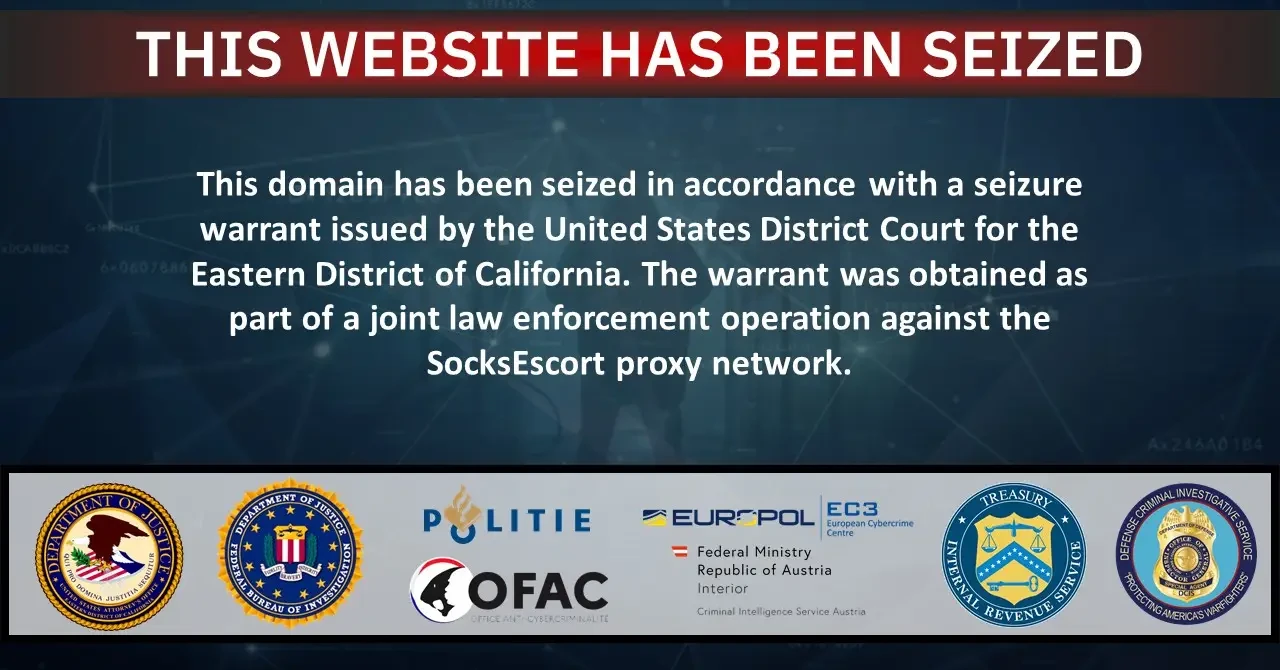
While authorities had been aware of the botnet for some time, official investigations were reportedly only launched by Europol in June of 2025. What adds to the confusion is that, despite Europol’s role, the operation was actually led by the U.S. Department of Justice (DOJ). Authorities from multiple countries participated in the operation, including the United States, Austria, France, the Netherlands, Germany, Romania, Hungary, and even Bulgaria.
As is often the case with such operations, specific details about the tactics and methods used remain undisclosed. However, the operation resulted in the seizure of 34 domains, 23 servers, and the forfeiture of $3.5 million in cryptocurrency. Despite the scale of the takedown, no arrests appear to have been made.
Conclusion
Not much is known about the tactics used in this operation. What we know is that digital finances, infrastructure, and domains have been seized, with no arrests made so far. As usual, depending on the contents of the servers, many arrests could follow. Depending on what information is stored on these servers, it could be a valuable resource, potentially helping to solve past cybercrimes.






























0 Comments