A serious data exposure incident involving Fiverr has recently been revealed, causing alarm among its user base. Fiverr, a popular platform for freelance work, is under scrutiny after a researcher uncovered that private user documents, including tax returns, driver’s licenses, and confidential work materials, were publicly accessible through Google Search. The company has denied any wrongdoing, asserting that this situation stems from a user-driven, marketplace activity and not a cybersecurity breach. However, the uncovered data has raised significant concerns about Fiverr's security practices and its handling of sensitive user information.
The Discovery of Leaked Data
The issue came to light when an anonymous security researcher, using the alias "morpheuskafka," disclosed the leak on a popular cybersecurity forum. The researcher claims to have reported the incident over 40 days ago but did not receive a response from Fiverr's security team. The leak involves sensitive documents stored on Cloudinary, a service Fiverr uses to manage files such as PDFs and images exchanged between buyers and sellers.
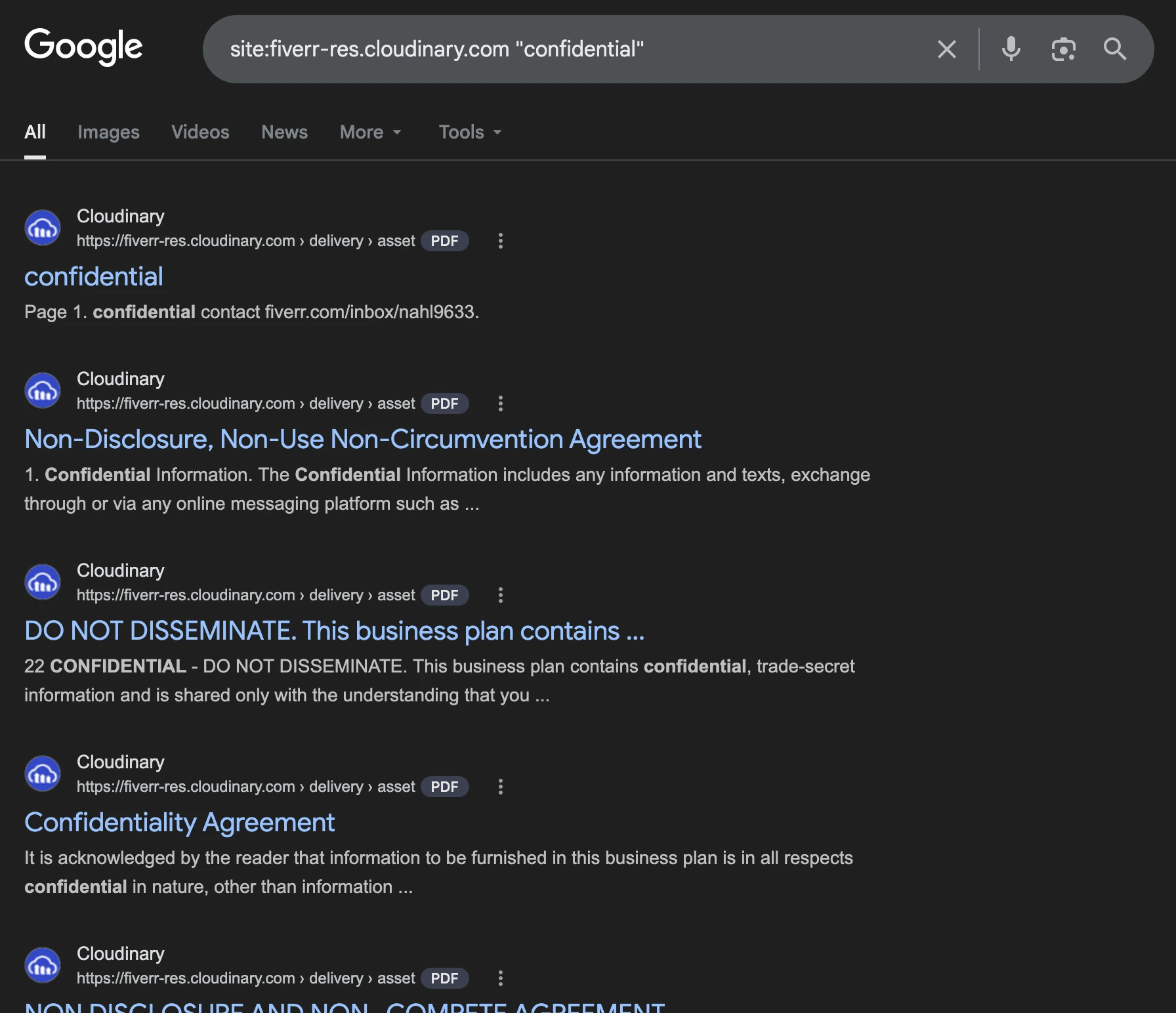
Cloudinary, much like Amazon’s S3 storage service, typically supports signed, expiring URLs for secure access to files. However, Fiverr allegedly opted to use publicly accessible URLs, leaving sensitive user documents exposed to anyone with the link. The situation worsened as these files were indexed by Google, making them searchable and accessible to the public. Among the files exposed were tax return forms, driver’s licenses, invoices, API keys, internal credentials, and even academic work such as graduate theses.
Fiverr's Response
In response to the claims, Fiverr has denied that a cybersecurity incident occurred. The company maintains that the exposed documents were shared by users as part of the normal marketplace activities, such as showcasing completed work samples, and that these files were uploaded with the buyer’s consent. Fiverr also emphasized that any requests to remove content are handled promptly, suggesting that users could request the deletion of sensitive data at any time.
Despite Fiverr's statement, the issue raises larger questions about its security policies, particularly when handling private user data. The company's response has been met with skepticism, especially considering that the leaked documents include highly sensitive personal information. Additionally, the exposure of Fiverr's own ISO 27001 certification—which expired four months ago—has cast further doubt on the platform's commitment to information security.
Some of the Leaked Data
The data exposed in the Fiverr leak ranges from tax returns and driver’s licenses to invoices, API keys. Even academic work such as graduate theses are included. Perhaps the most troubling aspect of the leak was how easily this sensitive information was accessed. Fiverr allegedly used public URLs for files shared between users, rather than employing secure, signed links that would expire after a set period. This reckless oversight allowed anyone with the correct link, including search engines like Google, to index these private documents. As a result, some of the leaked files were directly accessible via simple search queries, exposing personal and financial details that should have been safeguarded behind proper access controls. Including keywords like "confidential" and "passport" in search queries ironically filtered out some of the most sensitive data.
Concerns Over Data Privacy
The researcher claims to have responsibly disclosed the leak to Fiverr’s designated security email over a month ago, but received no reply. This delay in response has sparked frustration within the cybersecurity community, as many feel Fiverr failed to address the issue in a timely manner. Furthermore, the researcher pointed out that Fiverr's marketing practices may be compounding the problem. Fiverr has been purchasing Google Ads related to tax filing keywords, which could suggest that the platform is actively encouraging the sharing of sensitive financial information without sufficient security measures in place.
Given the exposure of such personal data, the incident may raise concerns under regulations like the Gramm-Leach-Bliley Act (GLBA), which mandates financial institutions to protect customer data. This breach could have serious legal implications, as Fiverr might be in violation of these data protection laws.
Ongoing Risk and Implications
While external actors cannot easily access the full list of affected files without the correct API keys, the researcher warns that the public availability of the files indexed by search engines poses a significant risk. Many of the exposed documents are now permanently indexed by Google, meaning that anyone can potentially retrieve them with simple search queries. This makes the situation particularly alarming, as personal identity documents, credentials, and work materials are often prime targets for exploitation.
The researcher has recommended that Fiverr users immediately rotate any credentials shared through the platform and monitor for signs of identity theft or unauthorized access to their accounts. Cybersecurity experts have called on Fiverr to implement stricter access controls to ensure that only authorized users can access private files. Additionally, Fiverr should audit the files that have been indexed by search engines and notify affected users of the breach.
Conclusion
The Fiverr data leak serves as a sobering reminder of the importance of secure data handling practices, particularly in the gig economy, where freelancers frequently exchange sensitive personal and work-related information. While Fiverr denies that a cybersecurity incident has occurred, the scale and nature of the data exposure suggest that the company’s current security protocols may be inadequate. As the situation unfolds, Fiverr will likely face increasing pressure to address these vulnerabilities and take responsibility for ensuring that user data is protected from future breaches.






























No comments yet — be the first.
Join the conversation
Log in to leave a comment