A dataset linked to Hallmark Cards, Inc. was leaked and is being circulated across cybercrime forums following a ransomware extortion attempt carried out by the infamous ransomware group ShinyHunters. The group issued a deadline in early April and later published data tied to the company after the deadline passed. The same dataset also appeared for sale on underground forums under a different alias, indicating multiple actors distributing identical material.
Extortion Timeline and Data Publication
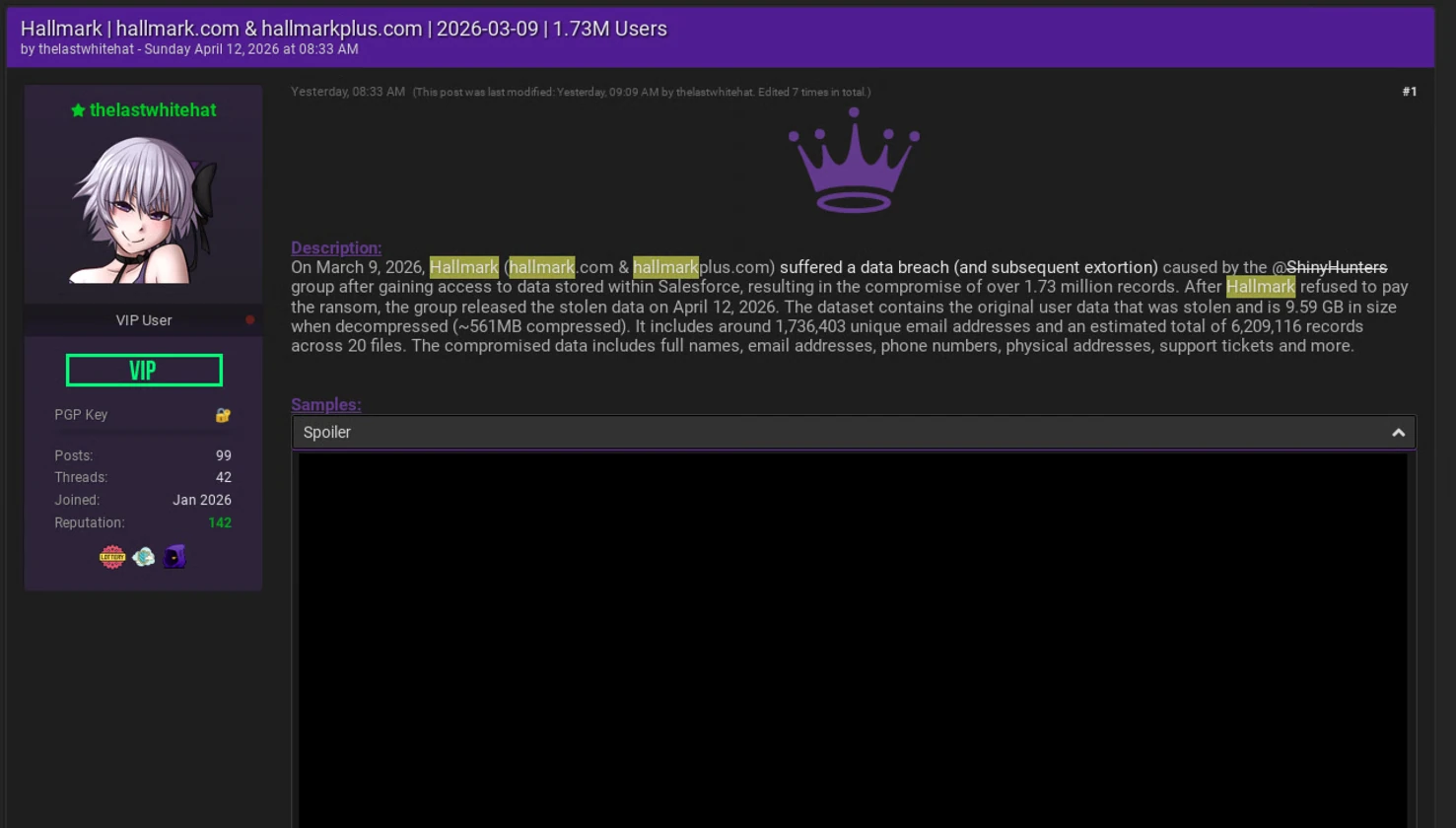
ShinyHunters targeted Hallmark Cards, Inc. and Hallmark Plus with a ransom demand involving nearly 8 million records. A deadline was set for April 2, after which the group published the data on its leak site. Following the publication, a separate actor listed what appears to be the same dataset for sale on a hacking forum. Analysis of sample records by cybernews confirms the datasets match, showing a single origin behind both the leak site publication and the marketplace listing.
Contents of the Exposed Dataset
The exposed dataset includes both customer and internal company information. Forum samples contain user-related records such as metadata fields, account flags, home addresses, and phone numbers in some cases. Additional entries originate from customer feedback systems and include ratings, comments, and related submission metadata. The full dataset published by ShinyHunters contains a broader set of information, including customer email addresses, corporate email accounts, employee names, departmental information, business hours, and customer support ticket records.
Source and System Access
The data is said by ShinyHunters to come from a Salesforce-related breach. The group claims the access was obtained through the Salesforce environment that has been linked to earlier large-scale intrusions affecting multiple organizations. ShinyHunters also state that the Hallmark data originates from this Salesforce breach activity rather than a separate, newly executed intrusion. It is not confirmed whether this incident involves a fresh compromise or data that was taken during earlier access and later reused or redistributed.
Exposure Risks and Exploitation
The dataset reportedly combines customer and employee information, creating conditions for targeted fraud and identity-based exploitation. Support ticket records and customer interaction data allow construction of convincing impersonation attempts based on real historical communications. The data can support phishing activity that uses internal language, service workflows, and prior support interactions to increase credibility in fraudulent communications.
Conclusion
Hallmark-related data is circulating across leak sites and underground forums following an extortion cycle tied to ShinyHunters. The dataset includes both customer and internal organizational records and is already distributed in multiple cybercrime channels. The origin remains tied to Salesforce-linked systems as stated by the actors involved, and the data is actively being reused and resold within underground markets. While still significant, this incident is not unusual for ShinyHunters, particularly given their recent high-profile activity, including the breach of the European Commission.






























0 Comments